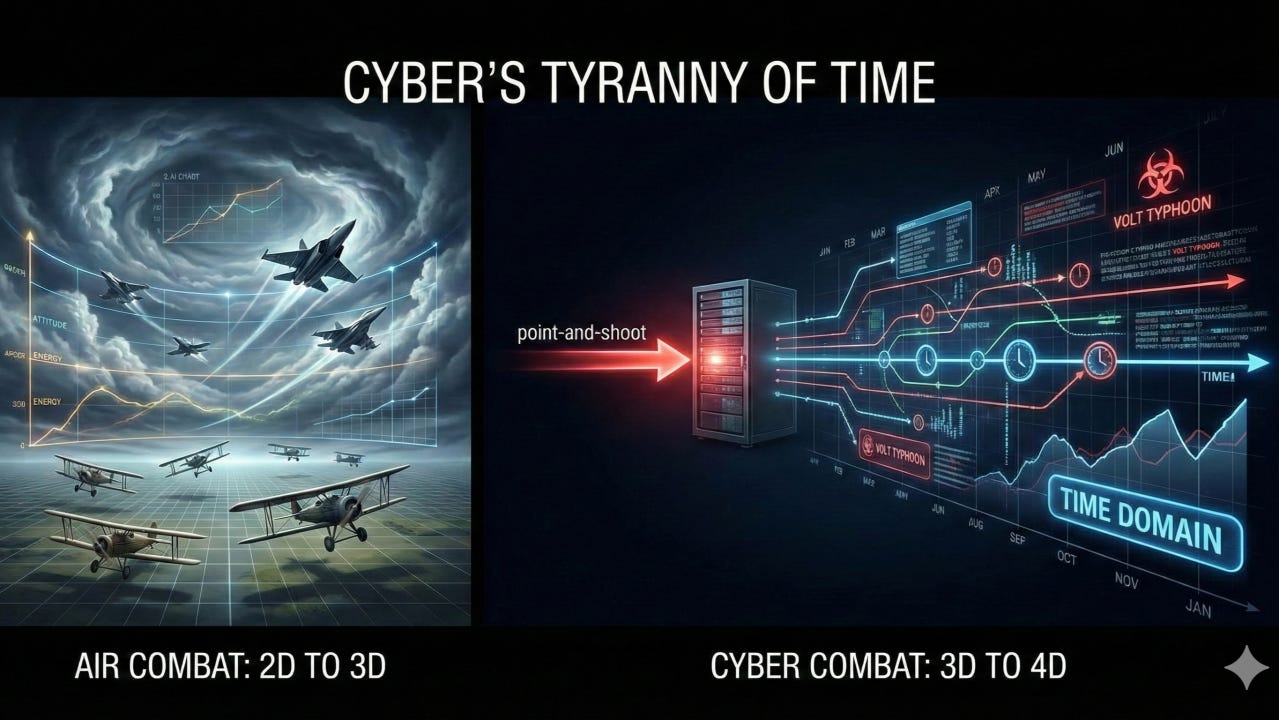
Cyber’s Tyranny of Time
Lessons from Air Combat: Two Dimensions to Three
A century ago, air combat went through a paradigm shift in understanding dimensionality which resulted in advanced tactics, platforms, and broad adoption beyond conducting intelligence for the more combined arms. During World War I’s early years, pilots intuitively thought of aerial warfare mostly in two-dimensional terms; i.e. maneuvering horizontally “above the ground.” They lacked established doctrines and largely learned by trial-and-error. As the war progressed, pioneering aviators like Oswald Boelcke articulated the crucial importance of the vertical dimension. Gaining altitude conferred a decisive energy advantage in dogfights, allowing pilots to dive on foes or disengage at will. In other words, the sky must be treated as a three-dimensional volume, not just a flat plane of maneuver. This intuitive leap in understanding led to new tactics (e.g. the dictum “secure the height advantage”) and drove successive generations of aircraft and then missiles focused on speed, climb rate, and agility to exploit the 3D battlespace. By the mid-20th century, these ad-hoc insights were unified by Col. John Boyd’s Energy–Maneuverability (E-M) theory. Boyd’s E-M theory provided a mathematical model of aircraft performance by combining altitude (potential energy), speed (kinetic energy), and other factors into a single framework. This allowed pilots and engineers to to quantify together how well an aircraft could maneuver or sustain energy in combat, rather than relying on gut feel alone. E-M charts plotted an aircraft’s energy performance across its flight envelope and made it easy to compare different designs. Boyd’s work not only explained why certain tactics worked, but also influenced platform development and resulting strategic planning. In short, air combat matured once it embraced all three spatial dimensions, aided by models that captured those dimensions rigorously.
Lessons from Cyber Combat: Three Dimensions to Four
Today’s cyberspace domain is undergoing a similar conceptual evolution, but the critical added dimension here is time (the “fourth dimension”). A common fallacy is to view cyber attacks or discrete phases in cyber attacks in a simplistic, three-dimensional “point-and-shoot” manner, as if they were instantaneous events akin to firing a speed-of-light cyber bullet at three dimensional key terrain. In this common perception of cyber, an attacker picks a target (e.g. a server at some IP address), points an exploit at a vulnerable service, and the target is immediately compromised. Everything is compressed into a single moment of attack, a bit like a Dirac delta impulse in physics and engineering (an idealized pulse of infinite magnitude at a single instant).
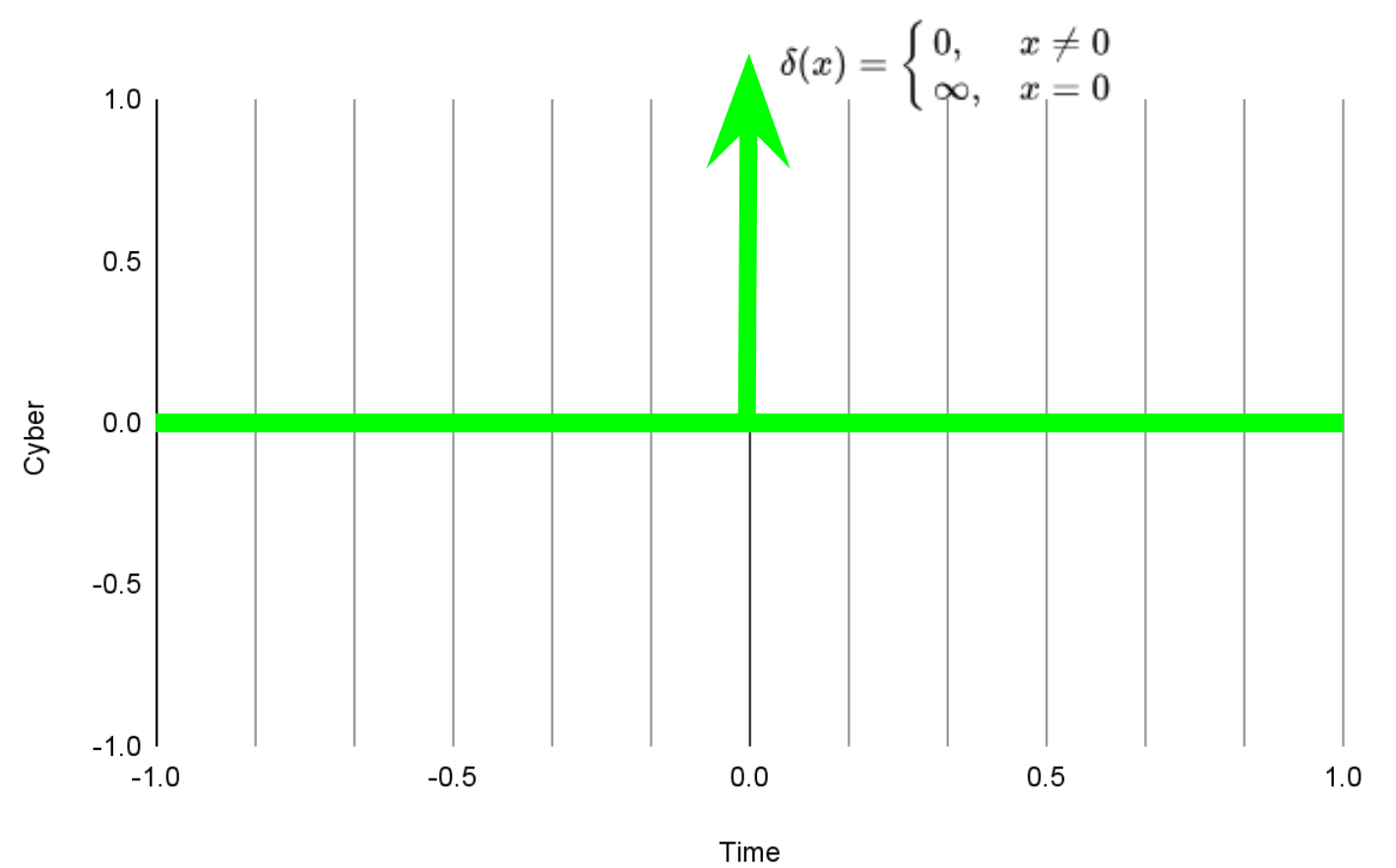
Likewise, “point-and-shoot” cyber is often imagined as a zero-duration, all-or-nothing event that happens in an instant or a kill chain that jumps between these dirac-like events. This mental model misrepresents reality. Discrete cyber maneuvers may appear instantaneous on human perception scales, but these maneuvers may occur over a very long time in computing. Conceptualizing cyber campaigns over imaginary time such as “the adversary maintained persistence for months” at worst is a single dirac impulse over “months” that glossed over the actual contest that happened in the domain. If we can’t articulate and model the time-domain contest then decisions rely on the disagreeing intuition of the few. This time-model of cyber is one of the things I will be working on during my sabbatical.
Cyber Operations as a Time-Domain Battle
Modern cyber warfare is fundamentally a contest in the time domain. Operations invest significant resources before and after the obvious operational moment to ensure their cyber effects succeed. For example, consider the exposed Volt Typhoon campaign. According to Microsoft threat intelligence, Volt Typhoon (a state-sponsored actor) infiltrated U.S. critical infrastructure networks as early as mid-2021 and maintained covert access for as long as possible without detection. The group focused on credential harvesting and network reconnaissance (“living off the land” tactics) to quietly persist over months or years, presumably so that they could deploy disruptive effects at a chosen time (e.g. during a geopolitical crisis).
Call it intelligence gathering, cyber ISR, Operational Preparation of the Environment (OPE), prepositioning, establishing access, an advanced persistence threat campaign, 0-day stockpiles, data lakes, credential dumps, etc. These are all examples of maneuvering in the time-domain.
Modeling Cyber in the Time Domain
If we look at these time-domain cyber maneuvers through Col Boyd’s lens it is reminiscent of his E-M theory and calculating Specific Excess Power (Ps).
Where:
V = Velocity
T = Thrust
D = Drag
W = Weight
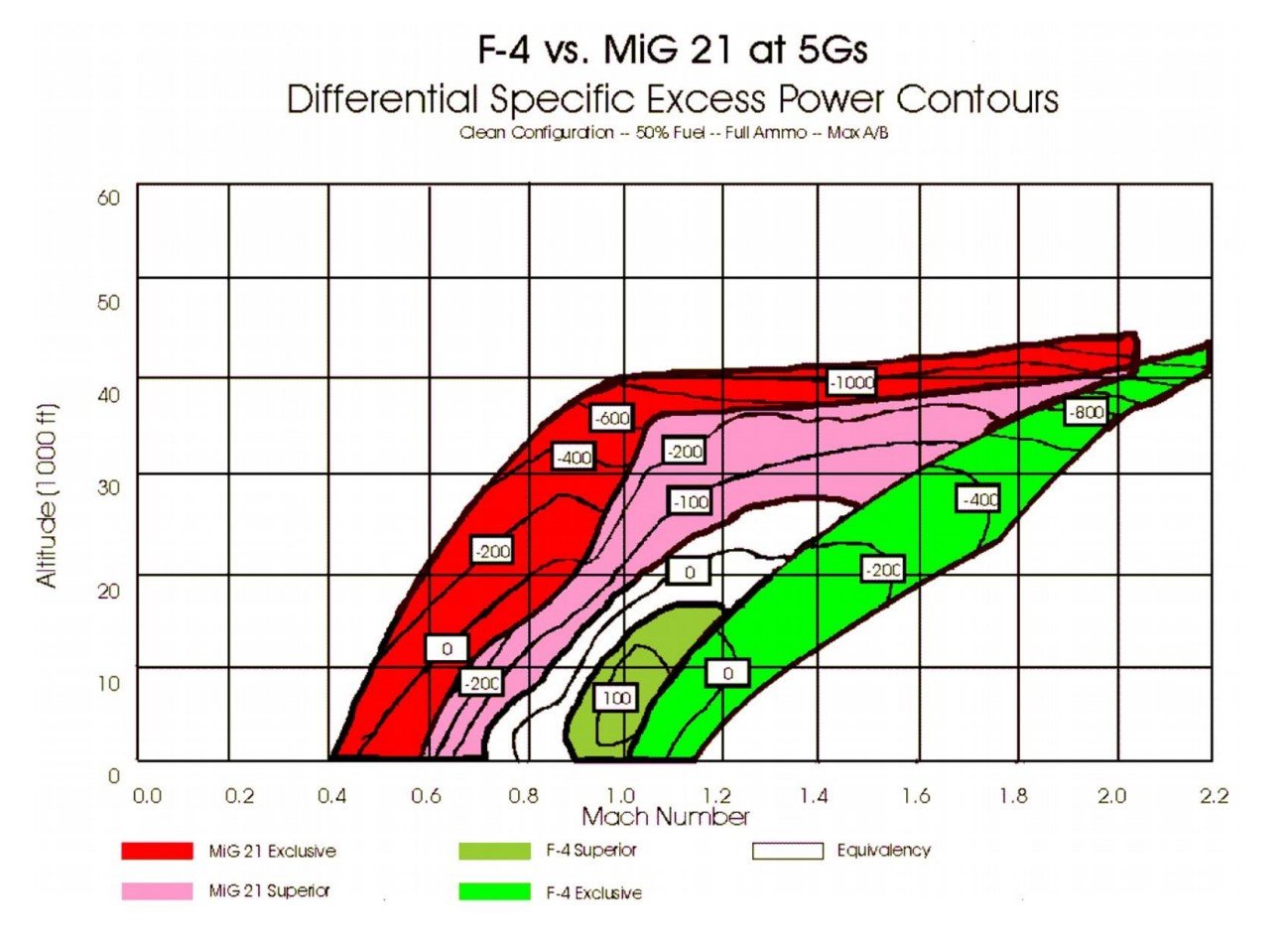
An aircraft with positive Ps can gain energy (speed or altitude). An aircraft with negative Ps is losing energy. According to Boyd, the pilot (or missile) who can maintain a higher energy state while maneuvering to a terminal position will win. Or more succinctly, the pilot trades altitude (potential energy) with velocity (kinetic energy). These can be represented as the below E-M graph of a F-4 vs a Mig 21 at 5gs (Source: USAF Academy Department of Aeronautics).
In three dimensional domains, a weapon must travel across space to affect a target which is often described in the tyranny of distance; and time is a function of distance. In cyber, we have no distance but contend with the tyranny of time. The cyber examples above are instances of managing the cyber potential energy such that they can be converted to kinetic energy; maneuvering in time not space. Would anyone argue against an 0day exploit stockpile or persistent access to critical infrastructure being Specific Cyber Power or would they just argue over it being Excess power?
During my sabbatical, I will be working towards a model where we can mathematically describe cyber, offense, and defense in the time domain. I hope to get to the place where we can mathematically graph the cyber domain such as the above E-M graph. And from there, I will start evaluating specific hypotheses and make some testable predictions. For example, I intuitively believe that 2026 offensive cyber and defensive cyber are not a zero-sum game. I hypothesize that they are two separate games which barely interact. Modeling those actual interactions and their strategic composition will hopefully help scale cyber past the artisanal towards where science, engineering, policy, and force generation are very effective; without having to fall back on an analogy to a more-rigorous domain.